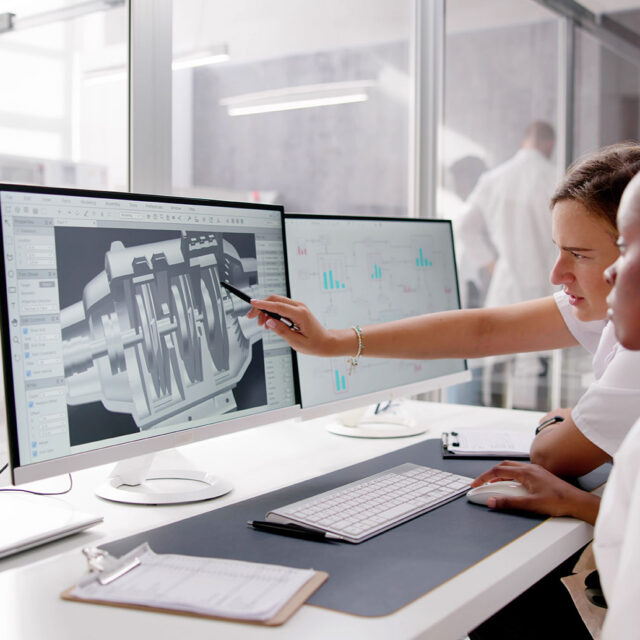
Virtual Live Courses & E-Learning
Synergie Training offers Virtual Training & E-Learning options designed for flexibility and accessibility. Our online courses allow professionals to gain valuable skills at their own pace, from any location—ideal for individuals or teams across all industries.